Context of the Organization and ITAR Compliance
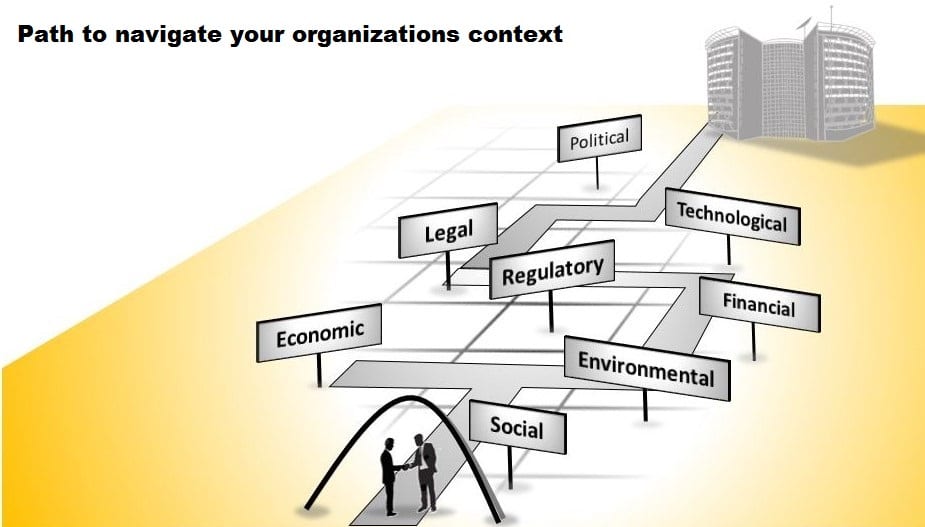
Utilizing the context of the organization clause of an ISO 9001:2015 Quality Management System (QMS) can allow for a more resilient ITAR compliance program. This can be accomplished by integrating export compliance into an existing management system s that includes all the tasks required to ensure that business is conducted in accordance to federal regulations. … Read more