The Disruptive Technology Task Force was launched in February of 2023 by the Department of Commerce, the Department of Justice, and the Federal Bureau of Investigation in an effort to prevent the unlawful acquisition of advanced technologies by foreign adversaries. To date this effort has resulted in numerous cases being filed against parties involved in sanctions and export control violations. These offenses involved the unlawful transfer of sensitive information, articles, and military-grade technology to China, Iran, and Russia.
Disruptive Technology Task Force Cases in 2023
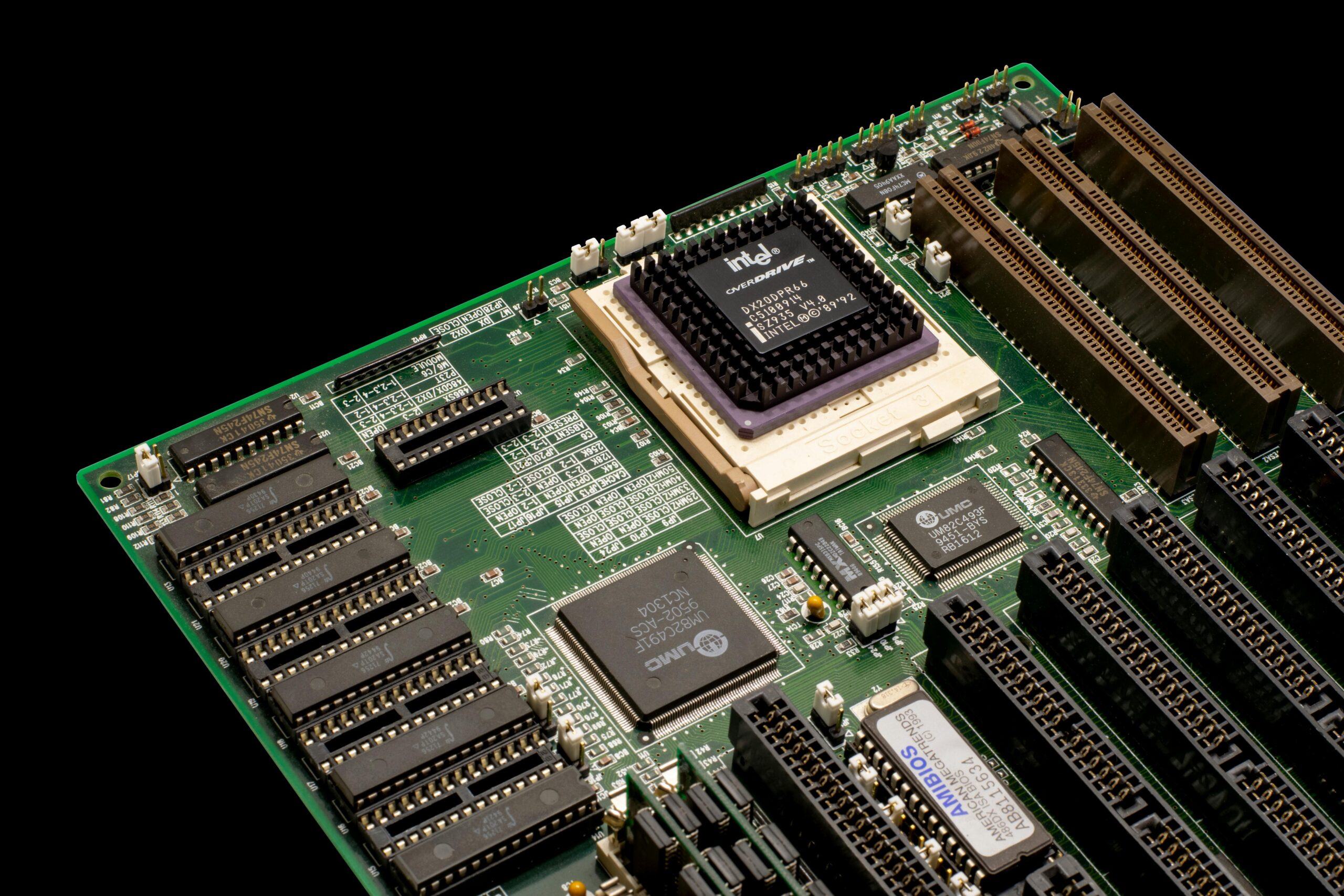
Half of the task force cases in the last year involved the attempted export of controlled semiconductors and microelectronics to Russia. Many of these included components for guided missile systems, Unmanned Aerial Vehicles (UAVs), components for weaponry, components used in cryptography, and nuclear weapons testing.
Cases involving exports to Russia were accomplished by the task force in partnership with the interagency law enforcement group, Task Force KleptoCapture. This group is comprised of agencies in the United States and its allies
Three cases involved individuals attempting to procure controlled technologies for Iran or Iranian end users. These cases involved items and technologies associated with military products, aerospace, firefighting, UAV’s, and materials used for weapons of mass destruction.
In an additional three cases, the task force charged former employees of U.S. companies with stealing proprietary and confidential information. These cases were all related to attempts to transfer advanced technologies to the People’s Republic of China. Technologies involved in these cases included missile detection equipment, advanced manufacturing software, and Apple source code. A fourth case involving a Belgian national, involved the export of military grade accelerometers.
Measures Taken to Enhance Enforcement
A number of partnerships have been formed to further enhance enforcement efforts.
- The Disruptive Task Force added the Defense Criminal Investigative Service as a formal partner.
- It added multi-agency enforcement teams to specific areas in the United States where critical technology industries are present.
- The Strike Force created a partnership with the Ukrainian Prosecutor General to curb the illegal flow of advanced technology to Russia.
- The Department of Commerce, Department of Justice, along with leaders from Japan and South Korea established a Disruptive Technology Protection Network to expand information sharing and best enforcement practices.
- The strike force fostered partnerships with the private sector to engage directly with companies involved in the manufacture and export of controlled items.
- Five Eyes export control agreement was formed to enhance the security concerns of Australia, Canada, New Zealand, the United Kingdom, and the United States by formally committing to coordinate export control enforcement efforts.
A Call to Actions for Businesses Involved in Export
The continued vigilance of the Disruptive Technology Strike Force enforcement illustrates the Bureau of Industry and Security’s (BIS) commitment protecting sensitive technologies. Besides partnering with U.S. enforcement agencies, the Commerce Department has shown a commitment to working with international agencies to protect national security and foreign policy concerns.
Enforcement activities have resulted in more severe civil and criminal penalties. In 2023, these activities have resulted in a record number of convictions, and denial orders. Additionally, numerous parties were placed on the Specially Designated Nationals, Blocked Persons, and Entity Lists, effectively ending their ability to conduct lawful business.
Businesses must ensure that they do not violate export regulations by enacting viable Export Compliance Management Programs (ECMP). These programs are a requirement for both the Export Administration Regulations and the International Traffic in Arms Regulations (ITAR). While most businesses involved with the ITAR have been proactive in compliance, many involved with the export of dual-use goods enumerated in the EAR have been less diligent.
Export Compliance Management Programs establish clearly defined policies and procedures for all departments within an organization. They ensure that registration, item classifications, license applications, denied part screening, and security measures are taken that will prevent violation. They also ensure that training, auditing, and record keeping are maintained according to requirements.
CVG Strategy Export Compliance Management Programs
Export Compliance is an important subject for businesses engaged in sales of items that are intended for international sales or could result in international sales. Failure to comply with export control laws can result in criminal prosecution including imprisonment and fines. It can also result in civil penalties and disbarment from export activities.
CVG Strategy can help you in understanding Export Administration Regulations and establishing a coherent and effective export compliance system. We can perform export control classifications, perform audits, and educate your team. Regardless of whether your business falls under EAR or ITAR, CVG Strategy has the expertise to help. Contact Us with you export regulation questions.