Bloomberg reported on February 12, 2021 that a Supermicro hardware hack had been conducted on server motherboards by a Chinese espionage program. This report follows previous reports by the news agency in 2018 and illustrates the susceptibility of technology manufacturers to supply chain attacks.
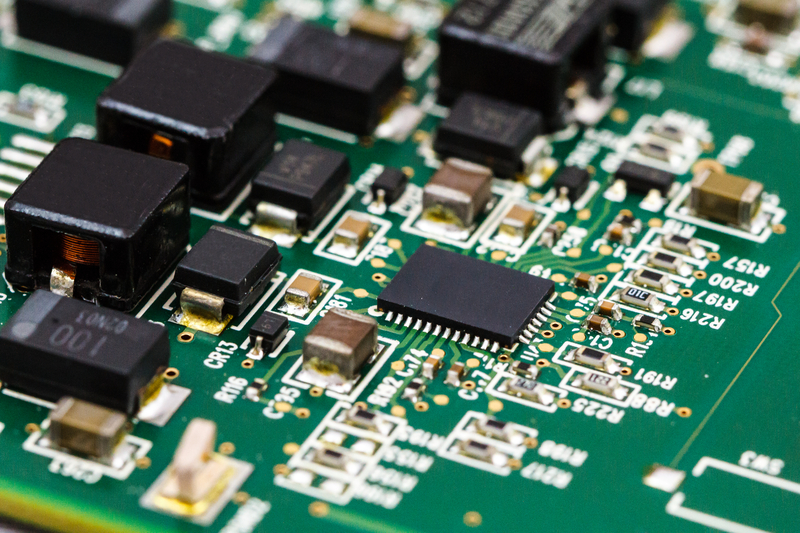
The hack involved embedding a small integrated circuit into the trace on a multilayered printed circuit board. This malicious hardware was inconspicuous enough to not be detected in quality assurance testing. Its purpose was to send data from the server to China. This hack has placed unknown numbers of data centers at risk in the public, private, and defense sectors at risk.
Spy Chips Found in Department of Defense Servers
In the Bloomberg article the United States Department of Defense (DoD) found that large numbers of its servers were sending data to China in 2010. Previous devices with malicious chips were found in Lenovo laptops used by the U.S. military in Iraq in 2008. It is not known how much data was compromised by these laptops in Iraq.
The incident in 2010 involved Supermicro servers on unclassified networks. While the implanted servers did not send any data regarding military operations, they did provide the Chinese with a partial map of the DoD’s unclassified networks. Supermicro has stated in response to questions that it had “never been contacted by the U.S. government, or by any of our customers, about these alleged investigations.”
According to Bloomberg sources security experts surmised that the implanted devices could be setting up networks for more extensive hacks or sabotaging entire networks in the event of a conflict between nations. In 2013 U.S. intelligence agencies including the National Security Agency decided to keep the discovery a secret, install countermeasures, and begin gathering intelligence on China’s motives without alerting it.
Supermicro Hacks Extend Beyond Hardware
Further investigations into the Pentagon breach ascertained that malicious instructions had been embedded in the servers’ BIOS, a set of instructions to the computer configuration that are executed during system start up. These types of malware are difficult to detect by means available even to users with good security protocols. These hacks were apparently conducted by Chinese agents early in product development.
Supermicro servers have also been exploited by a security breach generated by firmware updates generated from the company’s site. These breaches were detected by Intel security executives in 2014.
Hardware Hack and Supply Chain Vulnerabilities
This series of incidents point out the vulnerability to industry supply chains. Outsourcing manufacture of electronic assemblies to foreign countries is a common practice to reduce costs. However, business as usual may no longer be an acceptable practice.
U.S. government officials have in recent years been beating the drum about securing the supply chain, and while this may have immediate ramifications to the public and defense sectors, products destined for the private sector will continue to pose threats for network security and proprietary information.
Industry has been slow to engage in even basic cyber hygiene practices. Its willingness to apply stricter controls on its supply chain and manufacturing processes will be interesting to note. Clearly the Supermicro case along with the SolarWinds hack calls for a serious reassessment of industry protocols and diligence.
Challenges for Information Security Management Systems
Information Security Management Systems (ISMS) are a compilation of policies, procedures, and controls to identify and mitigate risk to data security. While incident response and asset management are features of these systems, assuring the security of the hardware, firmware, and bios of those assets provides sources of concern beyond the scope of many ISMS currently in place.
The National Security Agency (NSA) Cybersecurity Directorate has released Hardware and Firmware Security Guidance for aiding DoD administrators in the verification of systems currently in use. This repository is continually updated as new information and guidance become available.
Although this site is targeted towards the defense sector, it is applicable for organizations in the public sector as well. A list of hardware and firmware vulnerabilities can also be found in a post on INFOSEC which outlines a number of other vulnerabilities.
CVG Strategy Cybersecurity Solutions
Security of data is essential for any organization. This includes proprietary data, and the sensitive data of partners and customers. This latest report on the Supermicro hardware hack underlines the rapidly changing parameters of data security risks.
CVG Strategy is committed to helping businesses in all sectors, secure their sensitive data. We can help you meet your information security management system goals. CVG Strategy QMS experts are Exemplar Global Certified Lead Auditors.
We can provide the training required to understand and engage in a ISMS and make it meet desired objectives. This process includes defining the context of your organization, creation of internal auditing processes and much more.
The Department of Defense has been undertaking efforts to secure Unclassified Controlled Information (CUI) in its supply chain by the implementation of the Cybersecurity Maturity Model Certification (CMMC) program. CVG Strategy is helping DoD contractors prepare to for these requirements while meeting interim DFARS 252.204-7012 assessment requirements.